User activity documentation, particularly through Anoceligt and alerts logs, serves as a critical tool for organizations. These logs provide insights into user behavior and potential security threats. Anoceligt logs reveal trends in user interactions, while alerts logs signal anomalies that could indicate breaches. Understanding the interplay between these logs can enhance security measures significantly. However, the full implications of such monitoring extend beyond mere observation, raising questions about best practices and ethical considerations in user activity tracking.
The Significance of User Activity Documentation
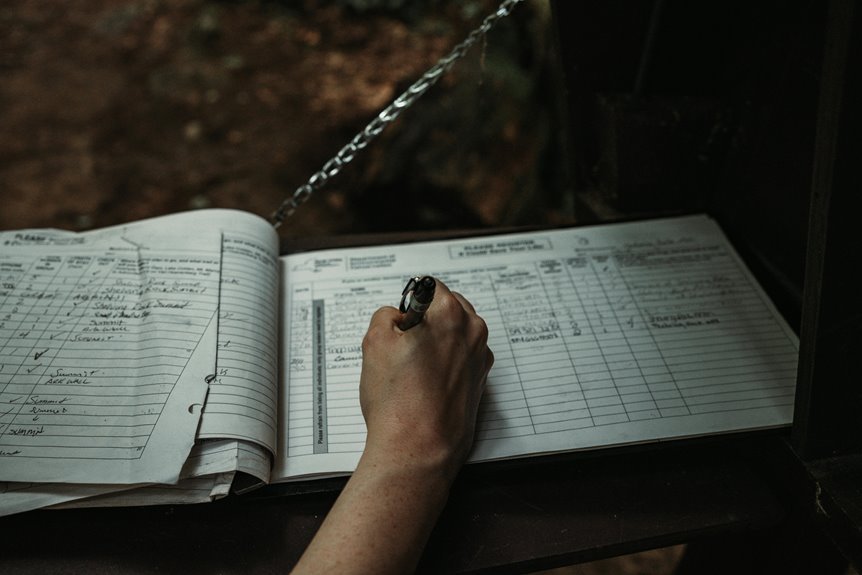
The significance of user activity documentation lies in its ability to provide a comprehensive understanding of user behavior within digital platforms.
By meticulously tracking interactions, organizations can ensure compliance with regulatory requirements while fostering user autonomy.
This documentation not only enhances security measures but also informs design improvements, ultimately empowering users to navigate platforms more effectively and with greater freedom.
Understanding Anoceligt Logs
How can organizations effectively leverage Anoceligt logs to enhance user experience and security?
Through meticulous anoceligt log analysis, they can identify user behavior patterns and discern trends that inform proactive strategies.
Analyzing Alerts Logs for Enhanced Security
Analyzing alerts logs serves as a critical component in bolstering organizational security measures.
By meticulously examining alert patterns, organizations can identify potential security breaches before they escalate. This proactive approach allows for the timely detection of anomalies, facilitating swift responses to threats.
Ultimately, a thorough analysis of alerts logs enhances an organization’s ability to maintain a secure environment while promoting operational freedom.
Best Practices for Effective User Activity Monitoring
Effective user activity monitoring is essential for maintaining robust security protocols within an organization.
Employing advanced monitoring tools enables the analysis of user behavior, facilitating the early identification of anomalies. Organizations should establish clear policies that outline acceptable use and ensure regular audits of monitoring practices.
This proactive approach not only safeguards sensitive data but also fosters a culture of trust and accountability among users.
Conclusion
In conclusion, user activity documentation, encompassing Anoceligt and alerts logs, is indispensable for organizations striving to bolster security and enhance user experience. These logs serve as a digital magnifying glass, revealing intricate patterns of user behavior and potential threats. By implementing best practices in monitoring, organizations can transform raw data into actionable insights, ensuring a proactive stance against security breaches. Ultimately, the integration of these logs fosters a culture of transparency and accountability, making the digital landscape safer for all.